
TASK 1 Key Terms
Read the words, and understand the meanings!
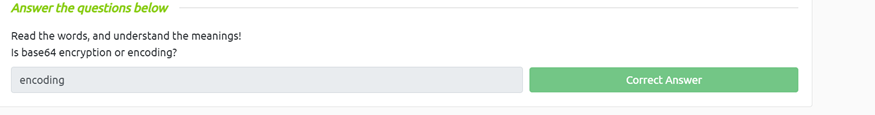
Is base64 encryption or encoding?
Since we read the terms we know Encoding is right because it says so, and base64 is immediately reversiable.
Task 2-What’s a hash function?
What is the output size in bytes of the MD5 hash function?
For this on we have to go to provided reading and we can find that the outputs size of the MD5 hash is 16

Can you avoid hash collisions? (Yea/Nay)
Through the reading we can cofidently say Nay, This is because with the hash being a preset length there are a limited amount of options which could cause a collision

If you have an 8-bit hash output, how many possible hashes exist?
So if we do the math with each bit having 2 options (1 or 0) and 8 bits we left with 2^8=256

Task 3-Uses For Hashing
Crack the hash “d0199f51d2728db6011945145a1b607a” using the rainbow table manually.
With the table provided, I just looked for the last 2 digits of the hash and table and then the first two and found the hash to be basketball.

Crack the hash “5b31f93c09ad1d065c0491b764d04933” using online tools
Using Md4hashing.net, it was able to spit out the hash of tryhackme

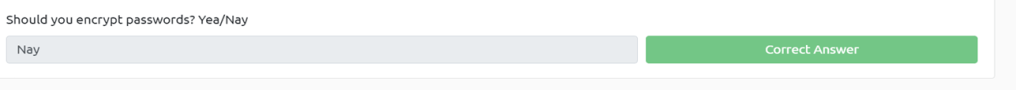
Should you encrypt passwords? Yea/Nay
The answer is no we should not encrypt passwords because if the encryption is broken, all the passwords are compromised instead we should hash them
Task 4- Recognising Hashes
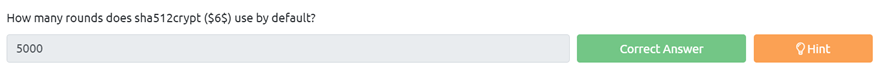
How many rounds does sha512crypt () use by default?
a quick Google search results with the soultion of 5000
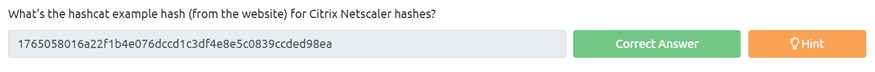
What’s the hashcat example hash (from the website) for Citrix Netscaler hashes?
Using the ctrl f and searching for netscaler we can find out it is 1765058016a22f1b4e076dccd1c3df4e8e5c0839ccded98ea

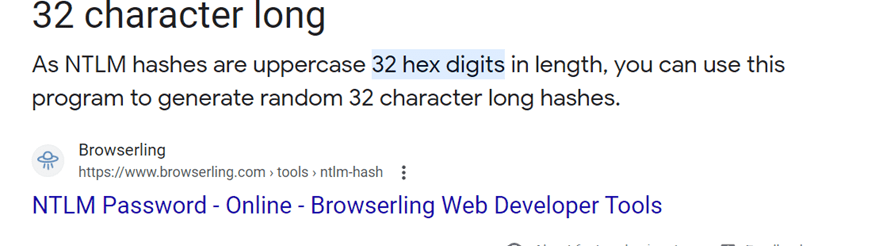
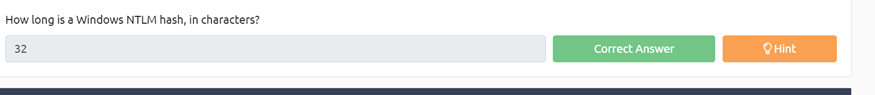
How long is a Windows NTLM hash, in characters?
A google seach tells us that ist 32 hex digits that are uppercase
Task 5- Password Cracking
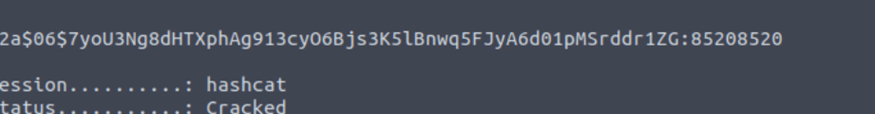
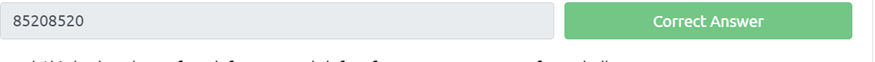
Crack this hash: $2a$06$7yoU3Ng8dHTXphAg913cyO6Bjs3K5lBnwq5FJyA6d01pMSrddr1ZG
So to crack this hash I used hash at and with some research came up ~#hashcat -a 0 -m 3200 (file directory)(wordlist directory) -w 3 -O -d 1
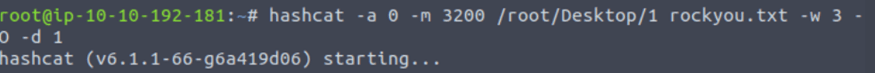
which returned
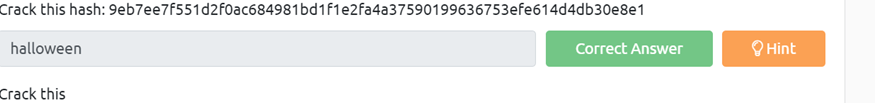
Crack this hash: 9eb7ee7f551d2f0ac684981bd1f1e2fa4a37590199636753efe614d4db30e8e1
For this hash I went with John and ran the command ~#john –wordlist(wordlist directory) –format=raw-sha256 (pass file location)

Than it returned

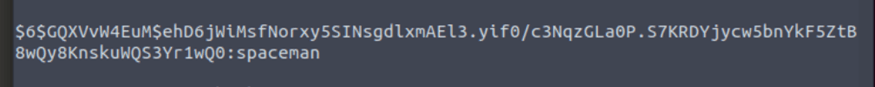
Crack this hash: GQXVvW4EuM$ehD6jWiMsfNorxy5SINsgdlxmAEl3.yif0/c3NqzGLa0P.S7KRDYjycw5bnYkF5ZtB8wQy8KnskuWQS3Yr1wQ0
I first noticed that it is a sha512crypt hash as noted by ‘$ 6 $”. I then saved the hash to my attack box desktop using touch hash.txt and copied the hash in. I then started hashcat and ran
~# hashcat -a 0 -m 1800 (file location) (password list location)

Which retrived
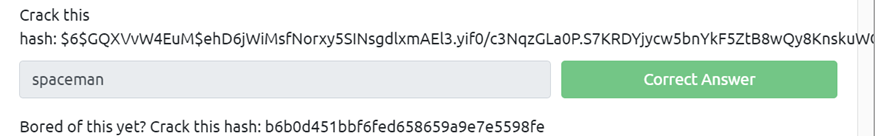
Bored of this yet? Crack this hash: b6b0d451bbf6fed658659a9e7e5598fe
I first tried hash cat running against a -a 0 option but it resulted in nothing so I went to the hashing toolkit online and ran it there and came up with funforyou


Task 6 Hashing for integrity checking
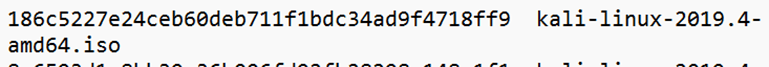
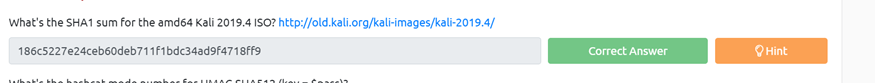
What’s the SHA1 sum for the amd64 Kali 2019.4 ISO? http://old.kali.org/kali-images/kali-2019.4/
Ok for this one was just going to click on the link and then find sha1 sums, then we will open the file amd64.iso hash which is 186c5227e24ceb60deb711f1bdc34ad9f4718ff
What’s the hashcat mode number for HMAC-SHA512 (key = $pass)?
For this one we will just go to https://hashcat.net/wiki/doku.php?id=example_hashes and look for the mode number which is 1750


And That is all there is for Hashing Crypto 101