Task 1 Deploy the Vulnerable Debian VM
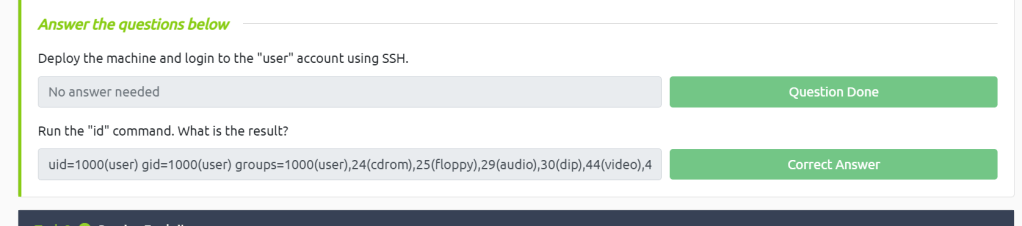
Deploy the machine and login to the “user” account using SSH.
Run the “id” command. What is the result?
This is pretty explanatory just run id.
Task 2 Service Exploits
Task 3 Weak File Permissions – Readable /etc/shadow
Answer the questions below
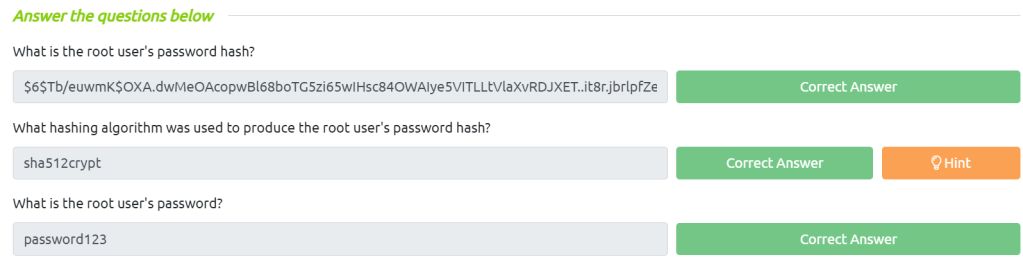
What is the root user’s password hash?
First on the target computer we need to dump the /etc/shadow file and save it to hash.txt on our attack machine then we can run john, john –wordlist=/usr/share/wordlists/rockyou.txt hash.txt, just remember that the hash doesn’t include the salt.
What hashing algorithm was used to produce the root user’s password hash?
If we do a little research on https://hashcat.net/wiki/doku.php?id=example_hashes we can find that the $6$ hash is a sha512crypt
What is the root user’s password?
For this we can just use john –wordlist=/usr/share/wordlists/rockyou.txt hash.txt
Task 4 Weak File Permissions – Writable /etc/shadow
Task 5 Weak File Permissions – Writable /etc/passwd
Run the “id” command as the newroot user. What is the result?
This is pretty easy first we need to see if the file is writable for us. So on our target machine we run ls -l /etc/passwd we can see it is. Next we just need to nano /etc/passwd and change the hash function to our hash. We can get the hash using open ssl passwd (newpass).
Task 6 Sudo – Shell Escape Sequences
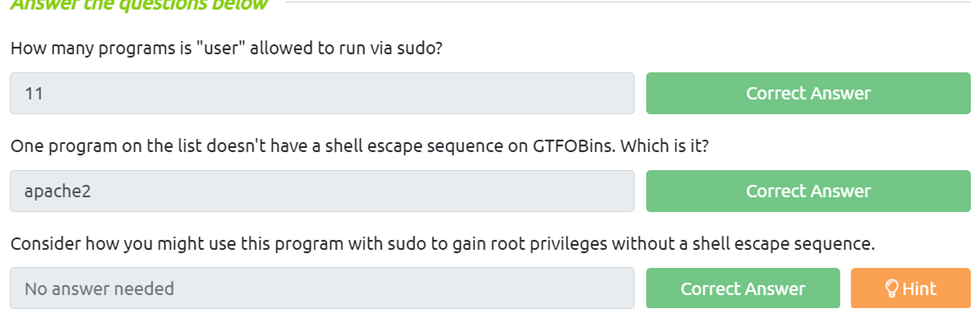
How many programs is “user” allowed to run via sudo?
We just neet to run sudo -l to list the programs we have sudo bit set for.
One program on the list doesn’t have a shell escape sequence on GTFOBins. Which is it?
All we need to do for this is go to gtfobins and compare programs.
Consider how you might use this program with sudo to gain root privileges without a shell escape sequence.
Task 7 Sudo – Environment Variables
Task 8 Cron Jobs – File Permissions
Task 9 Cron Jobs – PATH Environment Variable
What is the value of the PATH variable in /etc/crontab?
For this all we need to do is cat /etc/crontab and look for the PATH=/ varible
Task 10 Cron Jobs – Wildcards
Task 11 SUID / SGID Executables – Known Exploits
Task 12 SUID / SGID Executables – Shared Object Injection
Task 13 SUID / SGID Executables – Environment Variables
Task 14 SUID / SGID Executables – Abusing Shell Features (#1)
Task 15 SUID / SGID Executables – Abusing Shell Features (#2)
Task 16 Passwords & Keys – History Files
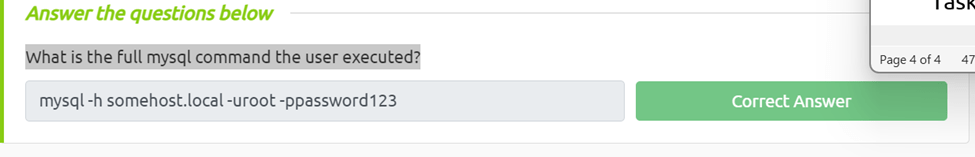
What is the full mysql command the user executed?
This ones pretty easy all we need to do is run cat ~/.*history | less
Task 17 Passwords & Keys – Config Files
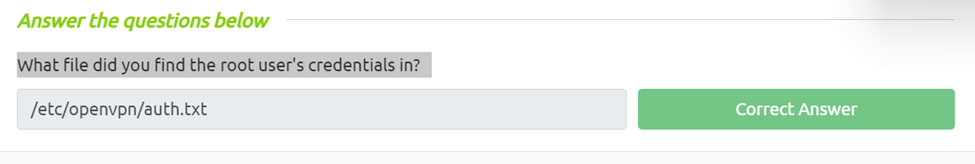
What file did you find the root user’s credentials in?
Again this is pretty basic we just need to cat /home/user/myvpn.ovpn and we can se a file that says auth user and password located at /etc/openvpn/auth.txt
Task 18 Passwords & Keys – SSH Keys
Task 19 NFS
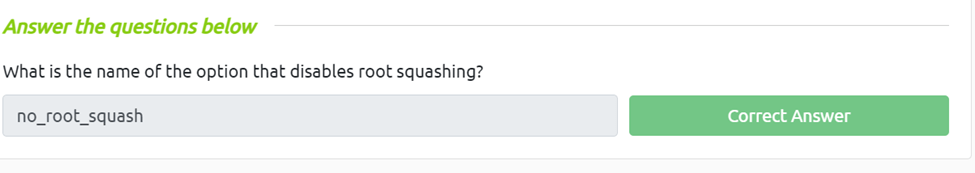
What is the name of the option that disables root squashing?
This is easy from our reading we can see the if the option is no_root_squashing using cat /etc/exports we know that root squashing is disabled and is vulnerable to several attacks.
Task 20 Kernel Exploits
Task 21 Privilege Escalation Scripts