Task 1 Introduction to MITRE
Task 2 Basic Terminology
Task 3 ATT&CK® Framework
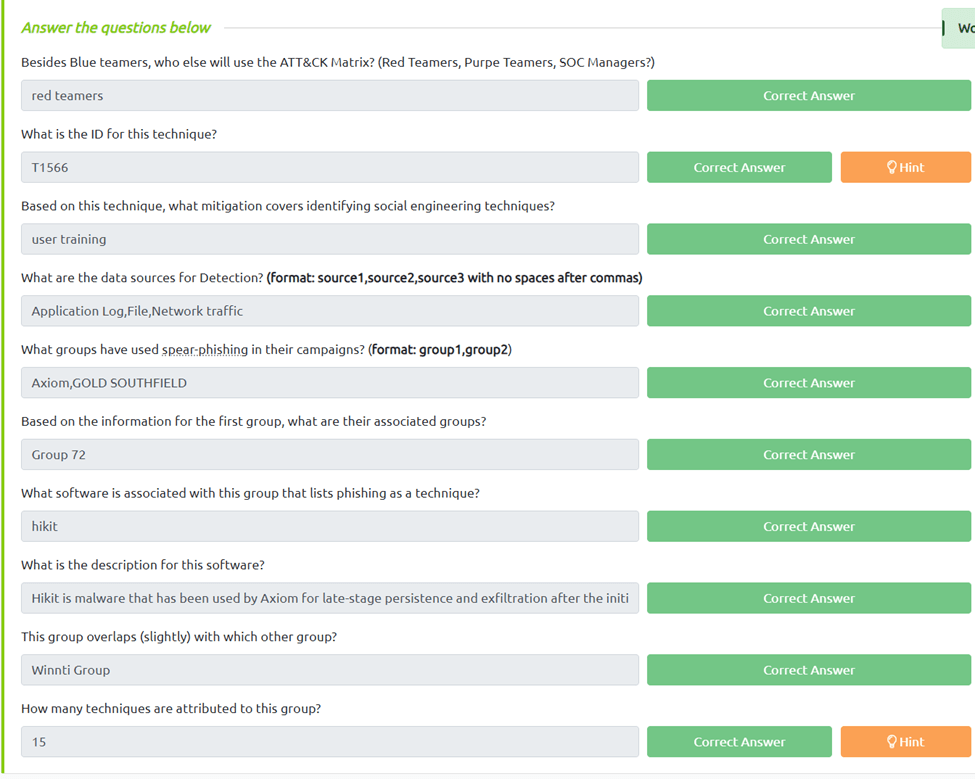
Besides Blue teamers, who else will use the ATT&CK Matrix? (Red Teamers, Purpe Teamers, SOC Managers?)
Our reading indicates red teamers can also use the ATT&ck framework
What is the ID for this technique?
If we go to the phishing page we can see the id of T1566
Based on this technique, what mitigation covers identifying social engineering techniques?
We can see user traing is the best mitigation effort for social engineering.
What are the data sources for Detection? (format: source1,source2,source3 with no spaces after commas)
IF we scroll down to detection we can see Application Log,File,Network Traffic
What groups have used spear-phishing in their campaigns? (format: group1,group2)
If we look under Procedure Examples we see Axiom,Gold Southfield use spear—phishing
Based on the information for the first group, what are their associated groups?
If we click on Axiom we get to see the associated group of Group 72
What software is associated with this group that lists phishing as a technique?
Back under Procedure examples we can see Hikit is the software.
What is the description for this software?
If we click on Hikit we get the description.,
This group overlaps (slightly) with which other group?
IF we click on Axiom we can see the Winnti Group overlaps with them.
How many techniques are attributed to this group?
When we count the Techniques used for Axiom we get 15
Task 4 CAR Knowledge Base
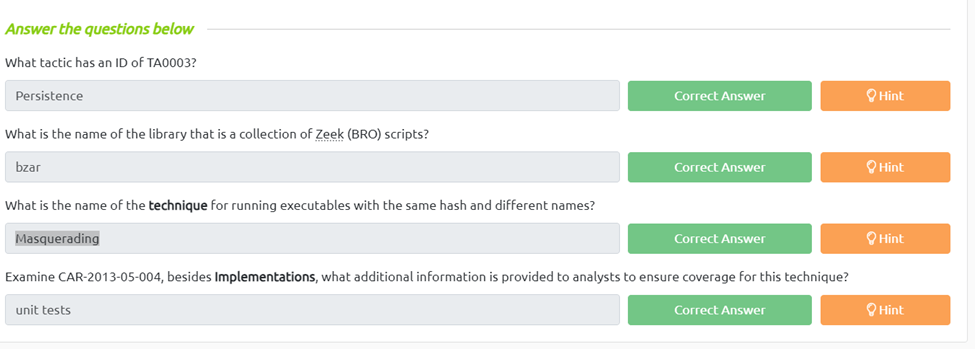
What tactic has an ID of TA0003?
To get this I clicked on the Execution tactic but its 0002, but it was the same in the url so I just changed it to 0003.
What is the name of the library that is a collection of Zeek (BRO) scripts?
If we look at the hint it says look at the main page and if we go there we can see there is only one library of zeek scripts and that’s BZAR.
What is the name of the technique for running executables with the same hash and different names?.
By going to the analytics page and using ctrl+f we can search hash and see that its Masquerading
Examine CAR-2013-05-004, besides Implementations, what additional information is provided to analysts to ensure coverage for this technique?
Looking at the Analytics page if we find the CAR we can click on that and if we scroll down we can see unit tests.
Task 5 MITRE Engage
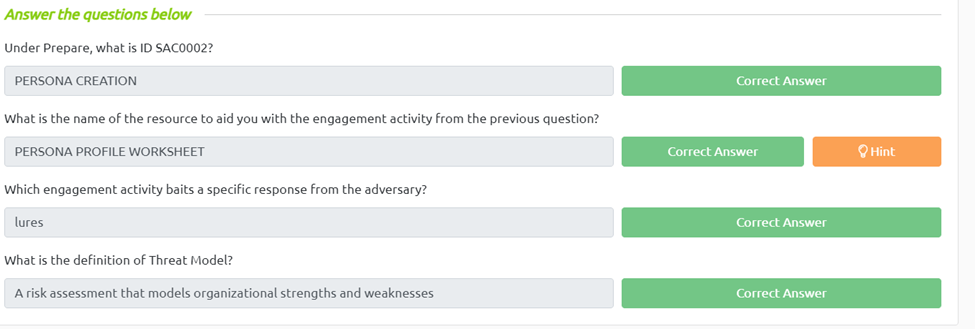
Under Prepare, what is ID SAC0002?
In the matrix under prepare we can see Persona Creation is SAC0002
What is the name of the resource to aid you with the engagement activity from the previous question?
If we click in to all tools we can see PERSONA PROFILE WORKSHEET would be the work sheet.
If we go into the matrix again and go to the operate tab under expose>detect we can see lures.
Which engagement activity baits a specific response from the adversary?
What is the definition of Threat Model?
Again in the matrix if we go to the Understand tabe we can can click threat model and it gives us our definition
Task 6 MITRE D3FEND
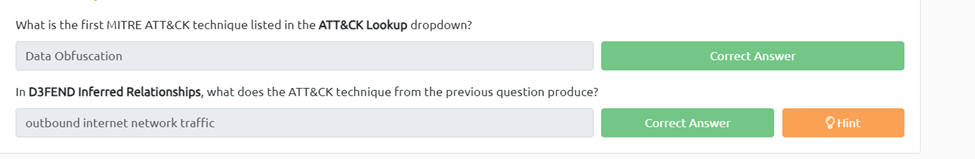
What is the first MITRE ATT&CK technique listed in the ATT&CK Lookup dropdown?
On the upper left we can see the ATT&ck Lookup box. If we click on that we data obfuscation
In D3FEND Inferred Relationships, what does the ATT&CK technique from the previous question produce?
If we click through into the data obfuscation we can see the inferred relationships and if we follow it through till the end we can see its outbound internet network traffic
Task 7 ATT&CK® Emulation Plans
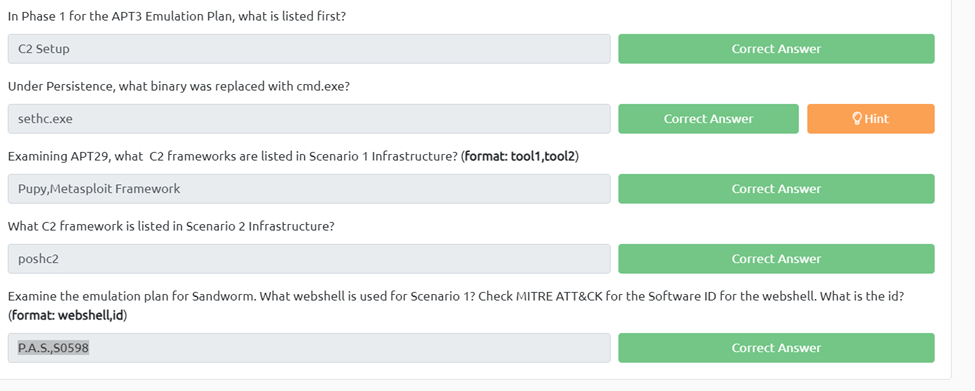
In Phase 1 for the APT3 Emulation Plan, what is listed first?
If we open up the APT3 plan we can see c2 setup is listed first
Under Persistence, what binary was replaced with cmd.exe?
If we open up the apt3 Plan and find persistence we can see sethc.exe is what is used to replace cmd.exe
Examining APT29, what C2 frameworks are listed in Scenario 1 Infrastructure? (format: tool1,tool2)
If we go into APT29>scenario 1 infrastructure we can see the c2 framework is Pupy,Metasploit Framework
What C2 framework is listed in Scenario 2 Infrastructure?
When we switch over to the scenario 2 infrastructure and search, we can see pashc2 is listed
Examine the emulation plan for Sandworm. What web shell is used for Scenario 1? Check MITRE ATT&CK for the Software ID for the web shell. What is the id? (format: webshell,id)
First, we need to navigate to sandworm/Emulation_Plan/Scenario_1 on GitHub. Now we see the P.A.S Web shell. Now if we go to the ATT&CK frame work and serach P.A.S we can see the id of s05989
Task 8 ATT&CK® and Threat Intelligence
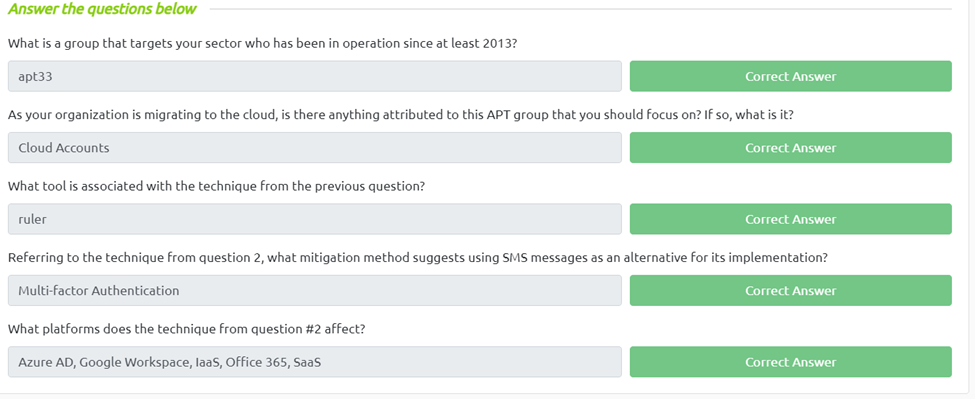
What is a group that targets your sector who has been in operation since at least 2013?
If we go to https://www.mandiant.com/resources/insights/apt-groups and ctrl+f we can search for aviation and we get apt33.
As your organization is migrating to the cloud, is there anything attributed to this APT group that you should focus on? If so, what is it?
Moving over to the ATT&CK platform and going to groups and selecting apt33 we can see Cloud accounts under techniques used.
What tool is associated with the technique from the previous question?
Looking In the description we can see apt33 used ruler to access cloud accounts.
Referring to the technique from question 2, what mitigation method suggests using SMS messages as an alternative for its implementation?
We can click into the cloud account page and we can see Multi-factor Authentication is recommended using SMS messages.
If we go in to cloud account
What platforms does the technique from question #2 affect?
On the top left of the cloud user page we can see the platforms Azure AD, Google Workspace, IaaS, Office 365, SaaS
Task 9 Conclusion