Task 1 Introduction
Task 2 Installation
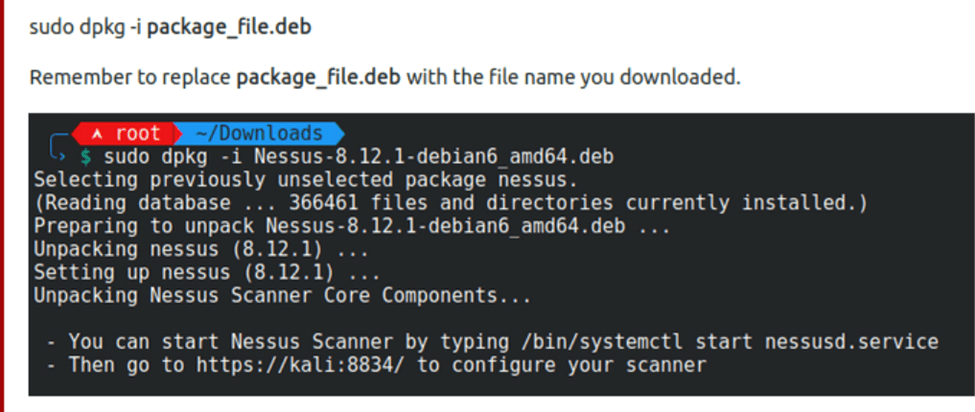
Just follow instructions here to download Nessus
If you want I just used “curl –request GET \
–url ‘https://www.tenable.com/downloads/api/v2/pages/nessus/files/Nessus-10.5.4-debian10_amd64.deb’ \
–output ‘Nessus-10.5.4-debian10_amd64.deb’´ for kali wsl2
I had an issue at this point because of using wsl2 however by running these commands I was able to solve it.
sudo apt-get update && sudo apt-get install -yqq daemonize dbus-user-session fontconfig
sudo daemonize /usr/bin/unshare –fork –pid –mount-proc /lib/systemd/systemd –system-unit=basic.target
exec sudo nsenter -t $(pidof systemd) -a su – $LOGNAME
snap version.
When you go to configure Nessus make sure you use the full path in the URL https://www.localhost:8834/#/
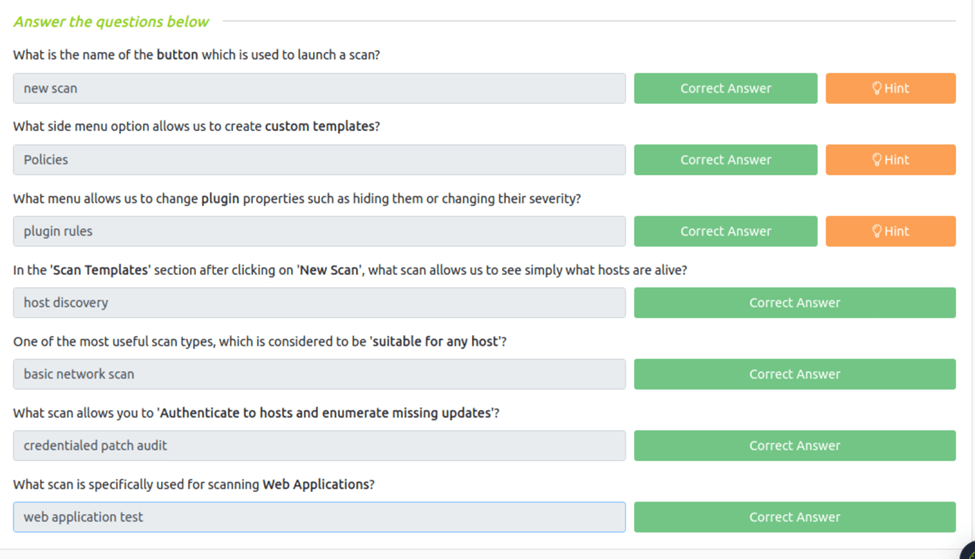
Task 3 Navigation and Scans
What is the name of the button which is used to launch a scan?
You have to click new scan to launch a scan
What side menu option allows us to create custom templates?
The policies option allows custom templates to be made
What menu allows us to change plugin properties such as hiding them or changing their severity?
You would use plugin rules to change the plugin properties
In the ‘Scan Templates’ section after clicking on ‘New Scan’, what scan allows us to see simply what hosts are alive?
Host discovery help find what host are alive.
One of the most useful scan types, which is considered to be ‘suitable for any host’?
The Basic Network Scan would be suitable for all hosts
What scan allows you to ‘Authenticate to hosts and enumerate missing updates’?
The credentialed patch audit would allow this.
What scan is specifically used for scanning Web Applications?
Web application test as the name implies
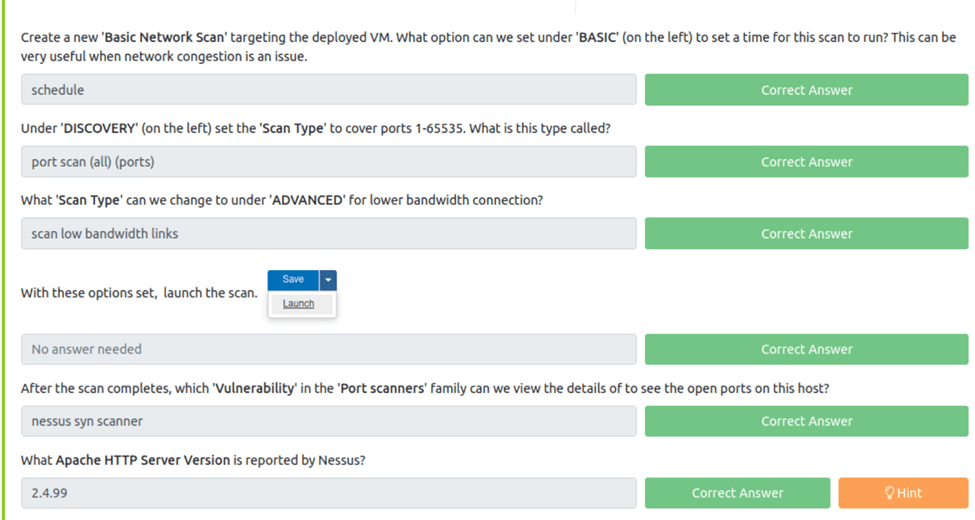
Task 4 Scanning!
Create a new ‘Basic Network Scan’ targeting the deployed VM. What option can we set under ‘BASIC’ (on the left) to set a time for this scan to run? This can be very useful when network congestion is an issue.
Obviously schedule would be the correct way.
Under ‘DISCOVERY’ (on the left) set the ‘Scan Type’ to cover ports 1-65535. What is this type called?
port scan (all) (ports) would cover all ports.
What ‘Scan Type’ can we change to under ‘ADVANCED’ for lower bandwidth connection?
After Navigating to advanced we can see scan low bandwidth links
With these options set, launch the scan.
After the scan completes, which ‘Vulnerability’ in the ‘Port scanners’ family can we view the details of to see the open ports on this host?
Make sure your connected to the THM server using openvpn instructions are here https://tryhackme.com/room/openvpn. But to find this we just run our scan and we can see nessus syn scanner is the vulnerability.
What Apache HTTP Server Version is reported by Nessus?
After our scan is complete if we look under the vulunablies tab we can see there is a apache http server version of 2.4.99
Task 5 Scanning a Web Application!
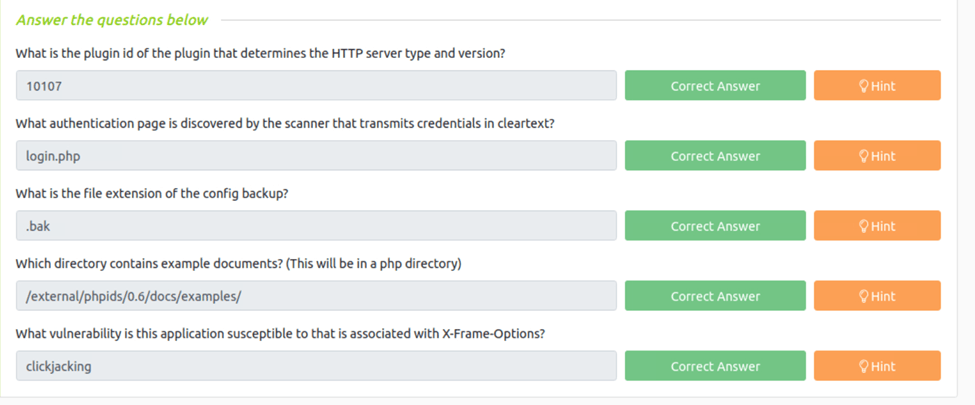
What is the plugin id of the plugin that determines the HTTP server type and version?
To find the plugin id we first need to go into vululablities then down to / HTTP (Multiple Issues). Now if we just hover over the http server type and version it gives us 10107
What authentication page is discovered by the scanner that transmits credentials in cleartext?
If we go to vulnerability and then to Web Server (Multiple Issues) we can then see Web Server Transmits Cleartext Credentials. If we click into that we see the page is login.php
What is the file extension of the config backup?
To get this we just need to go in vulnerabilities again and find the backup file disclosure. Once we click in to that we can see they are .bak files.
Which directory contains example documents? (This will be in a php directory)
If we just go into the vulnerabilities and then to Browsable Web Directories. If we look through the list we can see /external/phpids/0.6/docs/examples.
What vulnerability is this application susceptible to that is associated with X-Frame-Options?
If we navigate to the vulunablites and to the HTTP multiple issues. We can see a missing or permissive x frame. If we go into that we see that is susceptible to clickjacking.