Task 1 Brief
From our reading we can ansewre these easily.
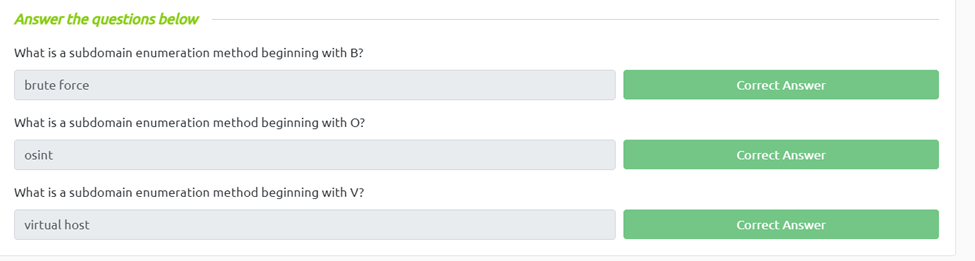
What is a subdomain enumeration method beginning with B?
bruteforce
What is a subdomain enumeration method beginning with O?
osint
What is a subdomain enumeration method beginning with V?
Virtual host
Task 2 OSINT – SSL/TLS Certificates
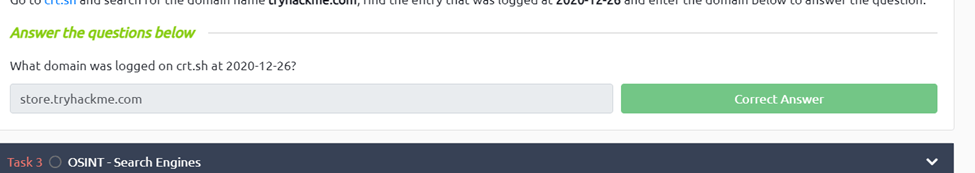
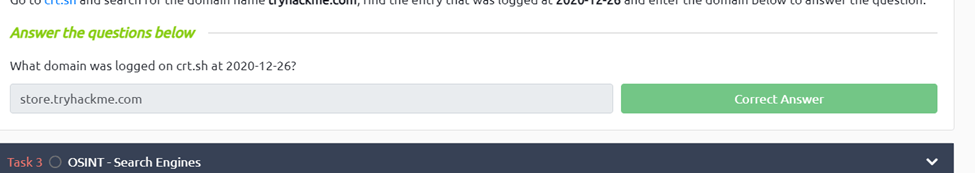
What domain was logged on crt.sh at 2020-12-26?
For this we just go to crt.sh and search tryhackme.com and scroll to 2020-12-26 and we can see store.tryhackme.com was logged.
Task 3 OSINT – Search Engines
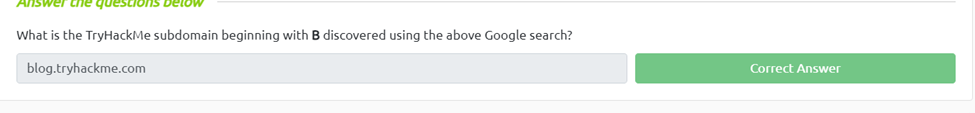
What is the TryHackMe subdomain beginning with B discovered using the above Google search?
Again this is pretty easy using the google dork -site:www.tryhackme.com site:*.tryhackme.com we can see blog.tryhackme.com pops up
Task 4 DNS Bruteforce
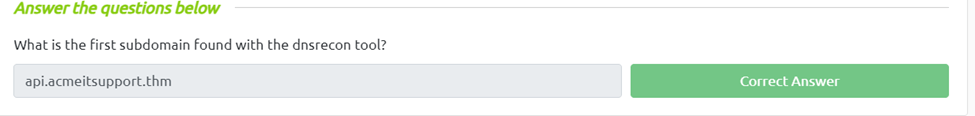
What is the first subdomain found with the dnsrecon tool?
All we need to do is click the open site and at the top of the right window pane we click run dnsrecon and we get 2 results including api.acmeitsupport.thm
Task 5 OSINT – Sublist3r
What is the first subdomain discovered by sublist3r?
Again for this one we click view site and then we just run ./sublister
And now we see the first domain listed is web55.acmeitsupport.thm
Task 6 Virtual Hosts
To get these well have to have our attack box and machine up and running. The next thing we can do is fuzz the given machine using the ffuf program. First we need to run “ffuf -w /usr/share/wordlists/SecLists/Discovery/DNS/namelist.txt -H “Host: FUZZ.acmeitsupport.thm” -u http://10.10.94.114” and if we notice the common file size is 2395 so then we can sort it to make our list more readable by running “ffuf -w /usr/share/wordlists/SecLists/Discovery/DNS/namelist.txt -H “Host: FUZZ.acmeitsupport.thm” -u http://10.10.94.114 -fs 2395”
And we can see some output
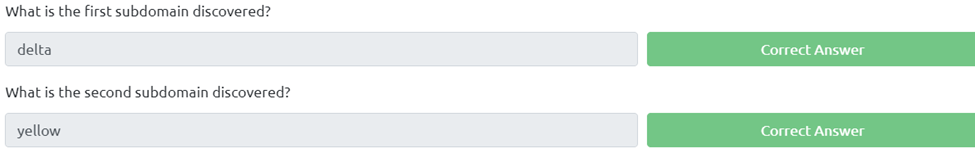
What is the first subdomain discovered?
delta
What is the second subdomain discovered?
Yellow